Stolen Credentials Don’t Have to Mean a Breach
Credential theft has become one of the most reliable and scalable attack methods today. Most environments still treat a correct login as proof of trust.
Learn more
Active Phishing Campaign in Medicine Hat… just in time for Christmas.
Just before Christmas, multiple organizations across Medicine Hat were targeted by a coordinated phishing campaign designed to steal Microsoft 365 email credentials.
Learn more
Vulnerability Scanning vs. Penetration Testing
Think of it like this: a vulnerability scan is your regular health check-up, while a penetration test is a simulated stress test to see how you perform under pressure.
Learn more
Backups Aren’t Enough: Why You Need a Full Disaster Recovery Plan
The question isn’t just “Do we have our data?” — it’s “How fast can we get back to work?”
Learn more
Getting a New Phone Over the Holidays? Don’t Forget This Crucial Step.
Unboxing and setting up a shiny new device? There’s one small, often-forgotten step that can cause big headaches when you’re back at work…
Learn more
The Apps and Tools You Don’t Know Your Staff Are Using
When employees can’t find an easy way to get work done, they often find their own.
Learn more
Why Employee Cybersecurity Training Matters
Cybersecurity isn’t just about firewalls and antivirus software — it’s about people.
Your employees are your first line of defense against cyber threats, but without training, they can also be your weakest link.
Learn more
If your password is Business2025!, We need to talk.
Still using passwords like Business2025!? They can be cracked in seconds. Learn how to create strong, secure passwords and why a password manager is essential for your business.
Learn more
Top 3 Strategies to Better Secure Your Business Technology (Right Now)
Email security breaches have become increasingly common, affecting organizations of all sizes and industries. These incidents not only highlight the vulnerabilities in email systems but also offer valuable lessons to prevent future attacks.
Learn more
What Is an MSP?
MSPs handle the technical foundation of a company—quietly managing infrastructure, reducing risks, and ensuring systems stay online.
Learn more
Preparing for AI—How We Make Businesses AI Ready in 90 Days
As AI reshapes business landscapes, the pressure to implement it swiftly and effectively is mounting. MSPs are uniquely positioned to guide this transformation—turning AI from aspiration into operational advantage.
Learn more
Is Your Business a Sitting Duck? How to Protect Yourself from Cyber Threats
Cyber threats are rising — is your business vulnerable? Learn how to protect your company from phishing, ransomware, and data breaches with simple, effective steps.
Learn more
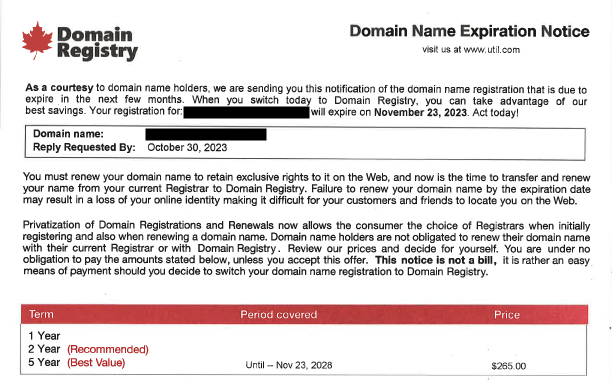
Beware of Domain Slamming: How to Spot and Stop the Scam
Learn how to identify and avoid domain slamming scams that trick businesses into overpaying for domain renewals.
Learn more
5 Rookie IT Mistakes Businesses Make – and How to Avoid Them
Email security breaches have become increasingly common, affecting organizations of all sizes and industries. These incidents not only highlight the vulnerabilities in email systems but also offer valuable lessons to prevent future attacks.
Learn more
Lessons from Real Email Security Incidents
Email security breaches have become increasingly common, affecting organizations of all sizes and industries. These incidents not only highlight the vulnerabilities in email systems but also offer valuable lessons to prevent future attacks.
Learn more
Email Security and Its Impact on Business Management
Beyond protecting sensitive information, robust email security practices contribute to operational efficiency, regulatory compliance, and overall business resilience.