Stolen Credentials Don’t Have to Mean a Breach
Credential theft has become one of the most reliable and scalable attack methods today. Most environments still treat a correct login as proof of trust.
Learn more
Why Sending Mass Emails from Your Inbox Is a Bad Idea
Sending mass emails from your inbox can create serious problems for your email system and for your business reputation.
Learn more
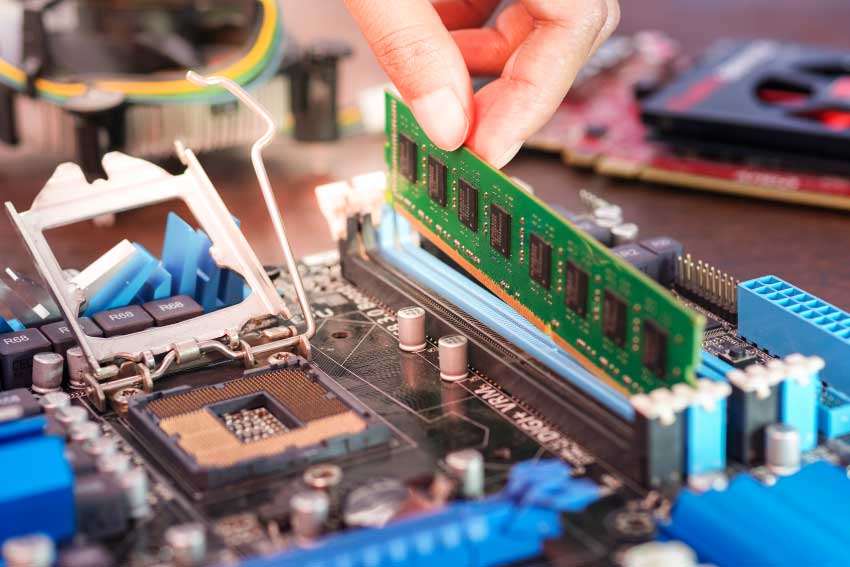
Why Business PC Prices Are Rising in 2026: The RAM Shortage and Supply Chain Reality
If you’ve recently priced out a new business computer, you may have noticed the cost of typical office PCs has gone up significantly.
Learn more
⚠️ Microsoft 365 Email and Services Outage
Thousands of users worldwide are reporting login errors, emails not sending/receiving, and general connectivity problems. Microsoft has officially acknowledged the issue and is actively investigating the cause.
Learn more
Vulnerability Scanning vs. Penetration Testing
Think of it like this: a vulnerability scan is your regular health check-up, while a penetration test is a simulated stress test to see how you perform under pressure.
Learn more
How Scalable IT Builds a Future-Ready Business
Your business isn’t static — it’s constantly evolving. If your technology can’t keep up, it becomes a bottleneck instead of a growth driver. That’s where scalable IT comes in.
Learn more
Backups Aren’t Enough: Why You Need a Full Disaster Recovery Plan
The question isn’t just “Do we have our data?” — it’s “How fast can we get back to work?”
Learn more
Getting a New Phone Over the Holidays? Don’t Forget This Crucial Step.
Unboxing and setting up a shiny new device? There’s one small, often-forgotten step that can cause big headaches when you’re back at work…
Learn more
The Apps and Tools You Don’t Know Your Staff Are Using
When employees can’t find an easy way to get work done, they often find their own.
Learn more
Why Employee Cybersecurity Training Matters
Cybersecurity isn’t just about firewalls and antivirus software — it’s about people.
Your employees are your first line of defense against cyber threats, but without training, they can also be your weakest link.
Learn more
The Hidden Cost of Downtime: How IT Outages Hurt Your Bottom Line
When your systems go down, so does your business. Whether it’s a server crash, an internet outage, or a ransomware attack, downtime doesn’t just interrupt your day — it directly impacts productivity, revenue, and customer trust.
Learn more
Why Domain Access Matters More Than You Think
We’ve seen firsthand how quickly things can unravel when a domain lapses or falls into the wrong hands — and how simple it can be to prevent.
Learn more
Is Your Tech Helping or Hurting Your Growth?
Outdated or scattered tech could be slowing your business down. Discover how the right tools and systems can boost productivity and support real growth.
Learn more
Are you wasting money on tech? How to cut costs without cutting corners
Learn how to reduce IT costs, eliminate waste, and streamline your tools — without sacrificing performance or security.
Learn more
Your Spreadsheet Looks Like It Went Through a Blender — The quick AI fix.
Messy spreadsheets full of typos, duplicates, and weird formatting? Learn how to clean up client data in seconds using Microsoft Copilot — and how Partek can help set it up.
Learn more
Still naming your files “Proposal-final-FINAL-version7”? — Your file chaos is costing you.
Tired of digging through emails to find the latest version of a file? Learn how SharePoint or OneDrive can end file confusion and streamline collaboration across your business.