What is Phishing?
“Phishing” can mean a handful of different things but generally encompasses all socially engineered email attacks, regardless of the specific malicious intent.
Here are a few of the other terms we use throughout this report and how we define them:
Bulk phishing:
High volume, indiscriminate, “commodity” attacks in which the same fraudulent email is sent to a large number of people within an organization. Although they are not tailored to the victim, they can be effective – if enough emails are sent, eventually someone will open one.
Phishing is like catching fish using a line — you cast your rod into the water and see what bites.
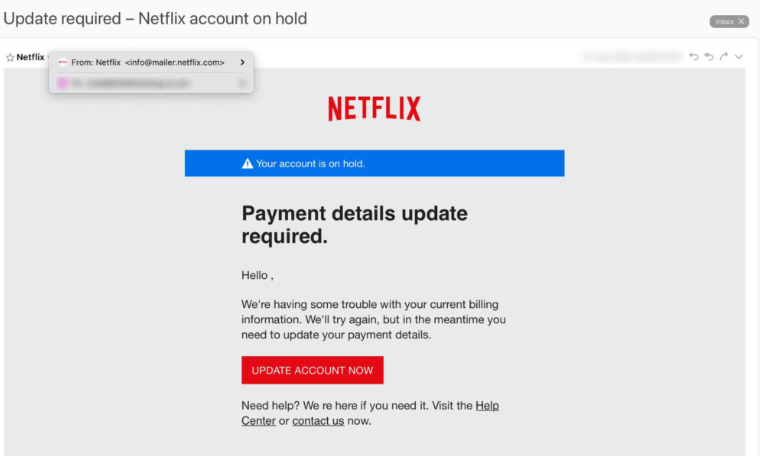
Example
Examples of bulk phishing attempts include emails relating to winning a prize, issues with the user’s account, or emails stating that a password has expired and needs to be changed.
This is an example of a “bulk” phishing email. It doesn’t address the target by name and doesn’t contain any personal information. But, because it appears to come from a trusted brand (Netflix) someone is likely to click the link.
Spear phishing:
Low volume, targeted attacks are sent to selected people within an organization. The cybercriminal has researched their target and uses personal information to tailor the attack. This type of phishing often sees more success, as an email containing personal information lowers the target’s guard, making them more likely to open a malicious link or file.
With spear phishing, you choose the fish you want and aim the spear right at it.
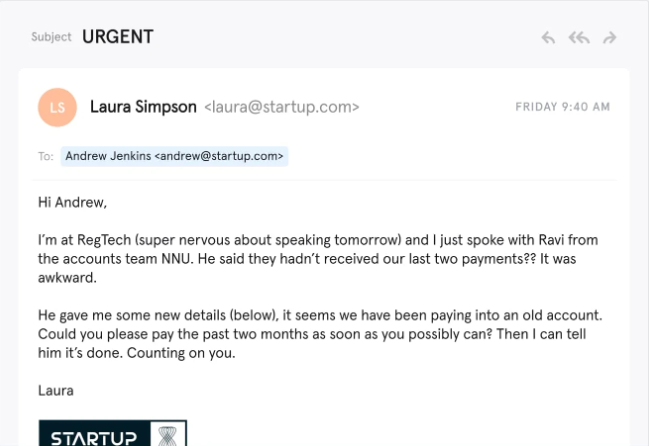
Example
These emails may include the victim’s name, or place of work, imitating a supplier or third-party technical support requiring the user to send their password for security purposes.
A common example of a spear phishing email is a request to update or change banking information. The attacker has exploited a professional relationship to elicit feelings of urgency and trust — the threat actor, acting as the CEO, urgently needs a favour and requests an employee to pay an invoice to an unknown account. Of course, the new account is actually controlled by the cyber criminal.
Whaling:
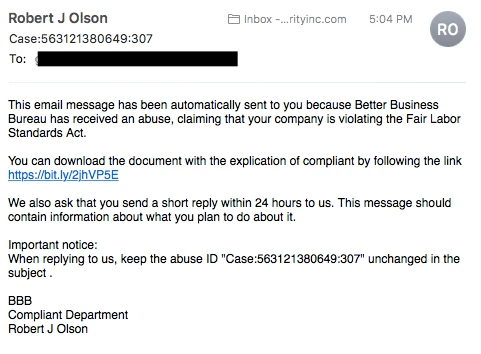
Attacks against high-value targets, such as top executives. If successful, Whaling attacks can be devastating for a company, as an executive’s account often has a high-level access to the network along with employee and customer data.Example
Threat actors may use a spear phishing attack to gain access to an employee’s email account, then use the employee’s account to phish an executive at the company. An executive has less reason to suspect a trusted email source, compared to an unknown individual.
In addition, a whaling email may indicate that the company is facing legal consequences and that the CEO must click on a fraudulent link to get more information. The link then takes them to a page where they are asked to enter critical data about the company, such as tax ID and bank account numbers.
Smishing:
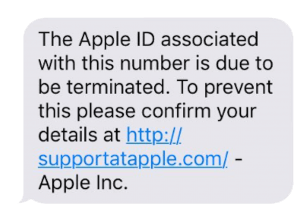
Attacks that use mobile text messaging (SMS) as the main communication vector.Example
A common example of a smishing attack is an SMS message that looks like it came from a trusted or familiar source.
It tells you your account has been compromised and that you need to respond immediately. The attacker asks you to verify your credential or confidential information often though a malicious link.
Vishing:
Attacks that use phone calls or voice messages to lure targets.Example
These are often messages imitating a bank or technical support asking for account information for security purposes.
A common vishing attack includes a call from someone claiming to be a representative from a trusted or familiar source. This person informs you that they’ve detected a virus on your computer and then requests your credit card details or remote access to your computer. The attacker explains they will install an “updated version of anti-virus software” on your computer. In reality, the attacker now has your credit card information, in addition to likely having installed malware on your computer.
before you go...
No related posts.